What?
Azure AD Dynamic Groups are populated with users or devices based on specific criteria defined in attribute based rules.
So What?
Dynamic group membership can be used to populate Security groups or Microsoft 365 Groups.
This functionality:
- Can reduce Administrative manual work effort.
- Can ensure that users or devices are assigned to the correct groups based on specified criteria.
- Can be used repeatedly for different membership scenarios which is defined by the rule syntax that is defined.
Now What?
Let’s review some details about Dynamic Groups
- You can create a Dynamic group for devices or for users, but you can’t create a rule that contains both users and devices.
- You can’t create a device group based on the device owners’ attributes. Device membership rules can only reference device attributes.
- Azure AD Premium P1 licenses are required for each user that is a member of one or more dynamic groups.
- Specific user license assignment is not required but minimum licenses are required in the Azure AD organization to accommodate dynamically assigned users. i.e. 100 users in one or more dynamic groups requires 100 licenses in organization.
- Devices in dynamic groups do not require licenses.
- The Dynamic groups rule builder supports up to 5 expressions. You can use advanced rules (text syntax) to create rules with more than 5 expressions.
- Total length of membership rule cannot exceed 3072 characters.
Configuring Rules
Dynamic groups use Properties, Operators and Values to construct a user or device rule.
A simple rule looks something like this:
user.physicalDeliveryOfficeName -eq “Head Quarters”
Where…
user.physicalDeliveryOfficeName = Property
-eq = Operator
“Head Quarters” = Value
Complex rules can have a combination of Operators
Operators listed below are in order of precedence from highest to lowest. Operators on same line are of equal precedence.
-eq -ne -startsWith -notStartsWith -contains -notContains -match –notMatch -in -notIn
-not
-and
-or
-any -all
More info on complex rules can be found in MS documentation for Dynamic Groups
Using Dynamic Groups and Rules (Examples)
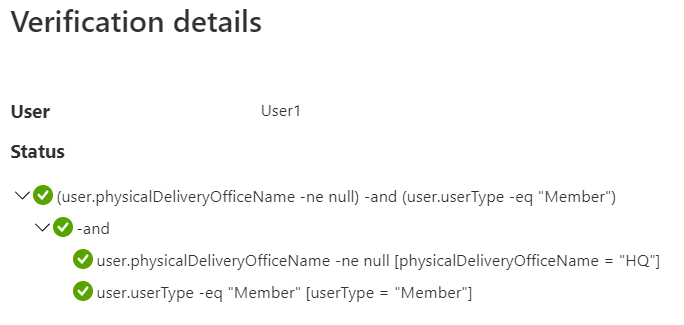
Example 1 – User’s Office location attribute is set and the user is an Azure AD member
(user.physicalDeliveryOfficeName -ne null) -and (user.userType -eq “Member”)
This rule can be used to exclude Guests and any user that does not have an office location attribute set. In the image below User1 satisfies both criteria.
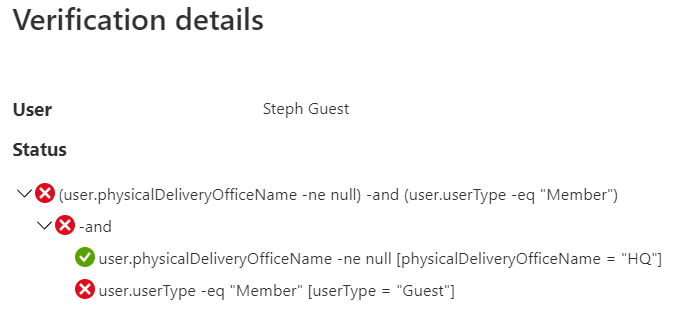
In this image the user satisfies the Office location attribute but does not satisfy the user type criteria.
Example 2 – User is directory synchronized, is not a guest and is assigned a specific Microsoft 365 service plan
(user.dirSyncEnabled -eq true) -and (user.userType -eq “Member”) -and (user.assignedPlans -any (assignedPlan.servicePlanId -eq “c1ec4a95-1f05-45b3-a911-aa3fa01094f5” -and assignedPlan.capabilityStatus -eq “Enabled”)
When a user or device fails to meet the defined membership rule that user or device will be removed from the group.
Dynamic Groups and Microsoft Teams
Learn how to use Dynamic groups to populate the membership of a Microsoft Team
How would you extend the second example to only show users that had been assigned the license within the last 24 hours?