
Hi! I’m Kayla, and I work at Regroove as the Senior Business Solutions Analyst. I work with organizations to implement cloud technology solutions that improve the way they work.
I’m also a Signals Officer in the Canadian Army Reserves.
Signals Officers are responsible for managing communication capabilities in the field, including information systems that assist with battlefield command and control.
You can bet the Canadian Armed Forces (CAF) has a strong security-minded culture, but you don’t have to handle national security to have a security-minded culture at your own organization. There are many aspects of security in the CAF that you can employ right now. Here are three tactics to keep in mind:
All Information Is Accessed on a Need-To-Know Basis.
Just because you’re the Commanding Officer or you have a top-secret security clearance does not mean you have a right to see every top-secret document. All information is need-to-know, and you need to prove your need to know before you can have access.

For organizations we work with, this typically translates to the concept of “least privilege access.” Least privilege access is the concept of restricting not only access to data, but administrative roles and functions assigned to a user account as well. This concept dictates that you should have access to the least amount of rights needed to effectively do your job.
In Azure, you can set up Privileged Identity Management (PIM) to manage access to functions or resources when they are required. Instead of having consistent access to data or functions, you are made eligible for a role and must activate that role for a specific period to accomplish tasks. An administrator can also set up an approval process so that management or IT is notified each time PIM is activated or is required to give approval before access is granted.
If you prefer not to implement PIM, you can create a version in your organization by ensuring that administrators or anyone required to have inconsistent access to administrative functions or important data have a specific admin account with these privileges. This mimics the concept by ensuring administrators need to log out of their regular account and purposefully log into their admin account before accessing important data or making administrative changes.
Fun fact – the US Department of Defence is credited for normalizing the concept of least privilege access!
All Information Should Be Labelled With Its Classification.
In the Army, that means that every file has a classification – think confidential, secret, top-secret – and is labelled with that designation. The classification or designation of a document begins with the person who creates it. They’re responsible for assessing the content to determine the security level required. Keep in mind that over-classification could impose impractical restrictions on the document, making it less accessible and efficient. Under-classification could fail to provide enough protection for the information, and when we’re talking about matters of national security or about personnel information, that can have pretty big consequences. Classification controls who can access the document, the level on encryption required for transmission, and where it can be stored.
We also use the concept of zoning to help determine where documents can be stored. Unclassified documents, for example, can sit on the reception desk, while top secret documents need to be in a high security zone where access is limited to authorized personnel.
You can apply all of these concepts to Microsoft 365.
Sensitivity labels let you classify and protect data by applying labels to files, emails, folders, and document libraries. You can even apply these labels to an entire site or team. There are many functions you can assign on a label, including extra encryption, access control, and watermarks that help identify the sensitive nature of the document. You can even automatically set labels using AI which determines what kind on content is included in the document.

You can also think of your sites and teams as security zones. Who should have access to these areas, and who has approval to grant that access? What can be “left on the desk” so to speak, and what, if anything, needs to be continually monitored? If you consider each of your SharePoint sites and Microsoft Teams as their own zone, it can be easier to determine what sites and teams you need in your environment and how to structure access to them.
Everyone Is Responsible for Security All the Time.
This is the most important concept to enable a security-minded culture in your organization. While this is drilled (literally) into you from the very start of your army career, it’s a concept we often find lacking at organizations we work with. From the co-op student you’ve hired for the summer to the CEO of your company, everyone is responsible for being mindful of security and taking steps to protect your data and information. You can (and should) talk about security at all hands meetings, company training events, newsletters, and every other chance you get to help reinforce the idea that everyone is responsible for security.
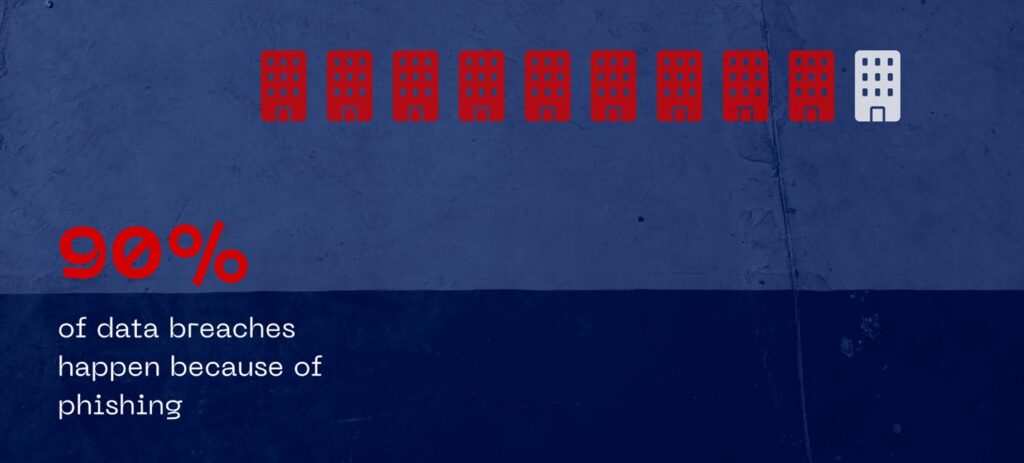
The most common forms of breaches are directly related to end user actions, such as ransomware and phishing attacks. In fact, 90% of data breaches at an organization are the result of a phishing attack. So, the first line of defence is your end users. It’s therefore just as important to create an environment where your team feels safe and comfortable admitting when they have made a mistake. An employee making a mistake and feeling scared to report it changes what could be a quick resolution to something much worse.
It’s not all up to the end user though. There are features in Microsoft 365 that help protect your end users at the individual level.
- Multifactor authentication is proven to prevent 99.9% of all incoming attacks. It’s relatively easy to implement and keeps security on the mind of your end users.
- Device management helps ensure that only authorized personnel and devices can access your company information and that all devices which access that information meet your organization’s security requirements. It also allows you to remotely wipe a company device’s contents if it is lost, stolen, or otherwise compromised.
- Attack simulation training allows you to send example phishing emails to your end users to demonstrate what these kinds of attacks look like. If the user clicks on the links in these emails, you’ll be notified, and can go so far as automating Microsoft training for the employee to complete. It seems harsh, but your security is worth it!
While my training with the CAF has certainly heightened my awareness and understanding of security, at Regroove, we’ve always been committed to helping our clients protect their end users and information with Microsoft 365. If you want to put security first at your organization, get in touch at [email protected]! We can start with a security assessment that will help define an organization-wide strategy.